In a world where Linux is no longer confined to servers tucked away in data centers, firewall security has become a daily concern for everyone—from students running Ubuntu on a laptop to system administrators managing cloud infrastructure. As Linux adoption grows across desktops, VPS hosting, and enterprise systems, the question of which firewall to use becomes increasingly relevant.
Two names dominate this conversation in 2026: UFW (Uncomplicated Firewall) and Firewalld. Both are powerful, widely used, and built on top of Linux’s underlying packet-filtering system. Yet they serve very different audiences and use cases.
This guide takes a practical, human approach to understanding UFW vs Firewalld—how they work, where they shine, where they fall short, and which one makes sense for you in today’s Linux ecosystem.
Table of Contents
Understanding Firewalls in Linux
At its core, a firewall is a gatekeeper. It decides which network traffic is allowed into your system and which is not. Linux firewalls operate by filtering packets based on rules—rules that can be defined by port, protocol, IP address, or interface.
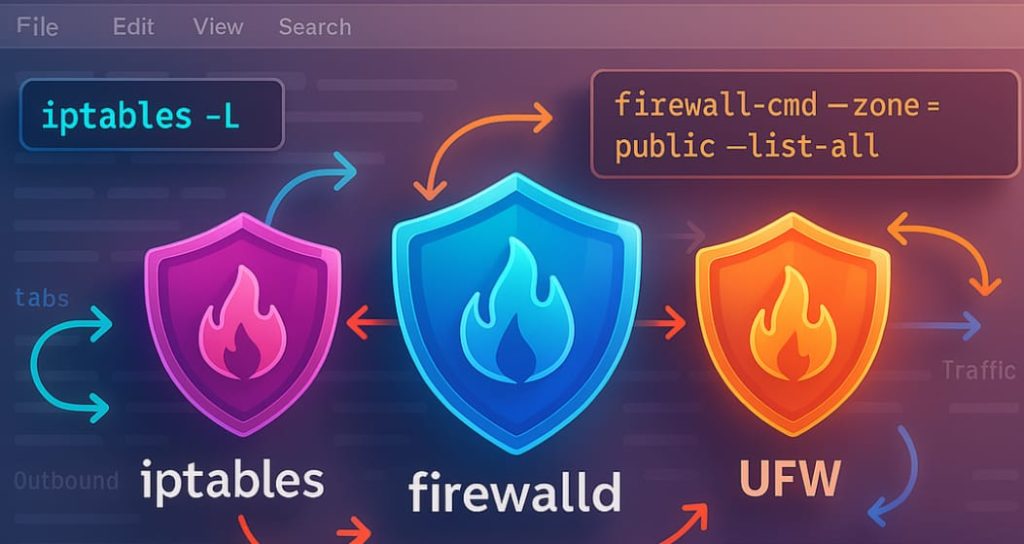
Modern Linux systems rely on Netfilter, a framework inside the Linux kernel that handles packet filtering. Tools like iptables, nftables, UFW, and Firewalld are essentially front-ends that help users interact with this system without writing complex kernel-level rules.
The real difference lies not in what they do, but in how they let users control network traffic.

What is UFW?
UFW, short for Uncomplicated Firewall, was created with a clear goal: make firewall management easy and accessible. Originally developed by Canonical for Ubuntu, UFW has since gained popularity across many Debian-based distributions.
UFW abstracts away the complexity of packet filtering and offers a straightforward command-line interface that feels almost conversational.
Why UFW exists
Linux firewall tools historically had a reputation for being intimidating. One wrong command could lock you out of your own system—especially on remote servers. UFW was designed to eliminate that fear by offering:
- Simple commands
- Sensible defaults
- Minimal configuration overhead
For many users, UFW is the first firewall they ever configure—and often the only one they need.
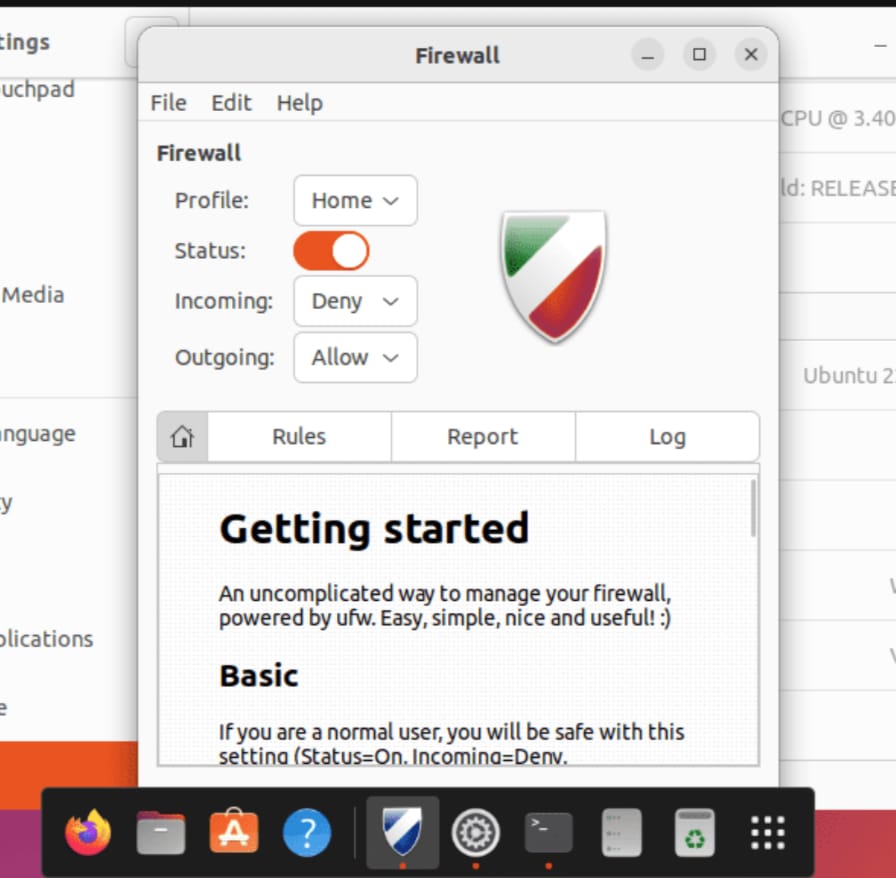
Key features of UFW
UFW is majorly focused on clarity and ease of use rather than deep customization.
- Simple rule syntax
Allow or deny traffic with plain language commands. - Default deny policy
Incoming connections are blocked by default, which aligns with good security practices. - IPv4 and IPv6 support
Both protocols are handled automatically. - Application profiles
Predefined rules for common services like OpenSSH or Apache. - Low learning curve
Even beginners can set up a basic firewall in minutes.
UFW works quietly in the background, doing its job without demanding constant attention.
Limitations of UFW
While UFW is simple,but that same simplicity can become a limitation.
- Limited dynamic rule handling
- Not ideal for complex networking setups
- Less flexible in enterprise or containerized environments
- Minimal runtime adjustments without reloads
In short, UFW is fantastic—until your networking needs grow beyond the basics.
What Is Firewalld? Dynamic and Powerful
Firewalld takes a very different approach. Rather than focusing on simplicity alone, it prioritizes flexibility, dynamism, and scalability. Firewalld is the default firewall solution on Red Hat–based distributions such as Fedora, RHEL, AlmaLinux, and Rocky Linux.
Instead of static rules, Firewalld uses zones, services, and runtime configurations, making it far more adaptable to changing network environments.
Understanding Firewalld
The major part of Firewalld is its zone system. A zone represents a level of trust assigned to a network connection.
Common zones include:
- Public – Untrusted networks (default)
- Home – Trusted local networks
- Work – Semi-trusted office environments
- Internal – Internal networks
- DMZ – Public-facing services
- Trusted – All traffic allowed
Each network interface can be assigned a zone, and each zone has its own rules. This allows Firewalld to adapt seamlessly when network conditions change.
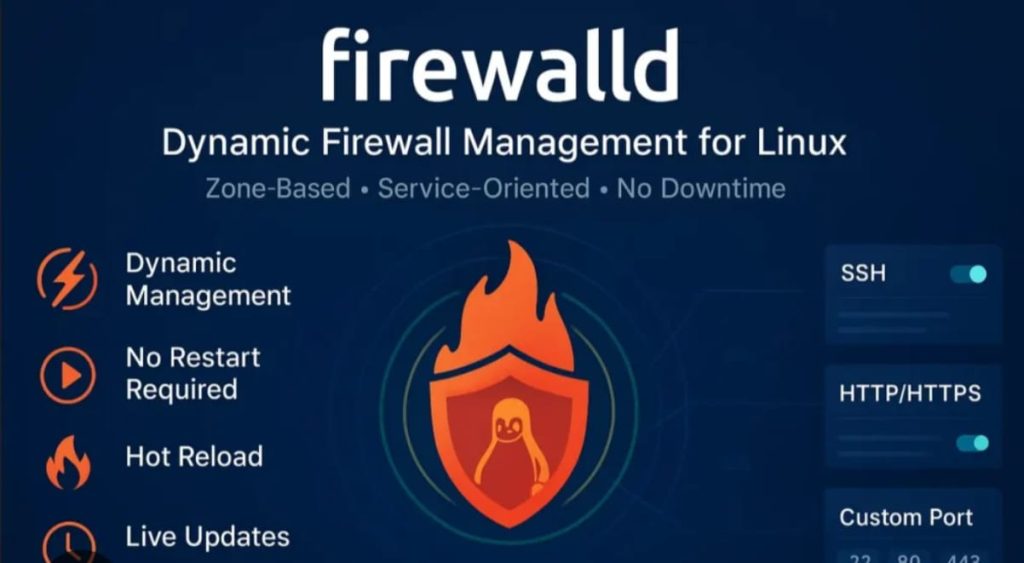
Key Features of Firewalld
Firewalld is designed for systems where network behavior is dynamic and complex. It is not as simple as UFW .
- Runtime rule changes
Modify rules without restarting the firewall. - Zone-based security
Different rules for different networks. - Service abstraction
Services are grouped by protocol and port. - Rich rules
Advanced filtering based on IP, protocol, and logging. - Native nftables support
Optimized for modern Linux kernels.
Firewalld doesn’t just protect a system—it adapts to it.
Challenges of Firewalld
Though powerful it comes with its own challenges .
- Steeper learning curve
- More concepts to understand (zones, services, rich rules)
- Can feel overwhelming for beginners
- Less intuitive for single-user desktops
Firewalld rewards patience and understanding, but it’s not plug-and-play.
UFW vs Firewalld: A Practical Comparison
Ease of Use
UFW wins hands down. Its commands are short, readable, and forgiving. Firewalld, while logical, requires users to understand its architecture before using it effectively.
Flexibility
Firewalld is far more flexible. It supports multiple interfaces, dynamic changes, and complex network setups. UFW is better suited for simpler environments.
Performance
Both tools perform efficiently on modern hardware. Differences are negligible for desktops and small servers. On large, complex systems, Firewalld scales better.
Which Firewall Should You Choose in 2026?
The answer depends less on trends and more on intent. As someone who is new to linux and wants quick and reliable protection and your network setup is simple then you should opt for UFW.
Whereas if you are working in enterprise or cloud environments which manages multiple interfaces .Your system runs services in different trust zones then you need Firewalld for powerful protection .
The State of Linux Firewalls in 2026
As Linux continues to evolve, firewall tools are becoming more intelligent, not just more complex. With nftables maturing and container security gaining importance, Firewalld aligns more naturally with modern infrastructure. At the same time, UFW remains a favorite for users who value clarity over control.
Security in 2026 isn’t about paranoia—it’s about intentional simplicity or intentional complexity, depending on your needs.

Conclusion
Firewalls are not about locking everything down—they’re about letting the right things through while keeping the rest out. UFW and Firewalld both succeed at this goal, but they speak different languages.
UFW speaks to individuals who want protection without friction. Firewalld speaks to administrators who need precision and adaptability.
Understanding both tools empowers you to make informed choices, not just follow defaults. And in a digital world where security is no longer optional, that understanding is your strongest defense.
What is the role of a firewall in a Linux system?
A firewall in a Linux system acts as a security barrier that controls incoming and outgoing network traffic. It decides which connections are allowed and which are blocked, helping protect the system from unauthorized access, malicious attacks, and accidental exposure of services, especially when connected to public or shared networks.
Why are Linux firewalls still important in 2026?
It remains important in 2026 because systems are constantly connected to the internet, cloud services, and public networks. Even personal laptops face security risks today. A firewall helps reduce these risks by limiting unnecessary access and ensuring only trusted traffic reaches the system.
What are the main advantages of using UFW?
The main advantages of UFW include its simplicity, clear command structure, safe default policies, and quick setup. Users can enable basic firewall protection within minutes without deep knowledge of networking, which makes it practical for everyday use.
What is Firewalld and how is it different from UFW?
Firewalld is a dynamic firewall management tool commonly used on Red Hat–based Linux distributions. Unlike UFW, it uses a zone-based model that allows different rules for different network environments, making it more flexible and suitable for modern, changing systems.
Why is Firewalld considered more powerful than UFW?
Firewalld is considered more powerful because it supports runtime rule changes, zone-based security, and advanced filtering options. These features make it suitable for enterprise systems, cloud environments, and servers that require flexible and scalable security management.
What challenges do users face when working with Firewalld?
The main challenge of Firewalld is its steep learning curve. It introduces several concepts such as zones, services, and rich rules, which can be confusing for beginners. Users often need more time and experience to use it confidently.
How do UFW and Firewalld reflect different approaches to Linux security?
UFW focuses on simplicity and ease of use, ensuring users can secure their systems without confusion. Firewalld focuses on adaptability and control, allowing administrators to manage security in complex and changing environments. Both approaches serve different but equally important needs.

Leave a Reply